Security-Sensitive BOM Lines Need a Sourcing File Before the RFQ
A tamper-aware or security-sensitive BOM line creates a procurement problem that is easy to underestimate. A part number may identify the device, package, and grade, but it does not always capture why that part is acceptable, what evidence should follow it, which alternates are already approved, or when a sourcing exception needs engineering and quality review.
The practical signal for buyers is straightforward: when a specific BOM line supports tamper-aware, trusted-supply, safety, infrastructure, defense-adjacent, medical, industrial-control, or other sensitive requirements, the sourcing conversation should start with a small evidence file rather than a bare MPN. That file does not replace inspection or engineering judgment. It gives procurement, quality, and engineering a shared reference before urgency pushes the decision into a narrow time window.
Why the sourcing file matters
Electronic Design recently discussed tamper detection and prevention in electronic systems, including physical attacks where someone has access to the device and may try methods such as glitching the power supply or clock. That is an engineering discussion, not a procurement instruction. But it illustrates why some board-level electronics cannot be sourced as if every quote is only a price-and-lead-time comparison.
For integrated circuits, memory, connectors, sensors, power management devices, FPGAs, microcontrollers, analog components, and discrete semiconductors used in sensitive products, the sourcing team needs to know what the design is trying to protect. A buyer does not need to become the security architect. The buyer does need enough context to avoid accepting an alternate, date code, package source, refurb condition, or documentation gap that conflicts with the product’s risk posture.
That is where a sourcing file helps. It turns security-sensitive design context into procurement acceptance criteria: which manufacturer part numbers are approved, which substitutions require review, which documents should accompany the shipment, which handling or packaging details matter, and who must approve exceptions.
What this means for PCX buyers
For PCX buyers, the issue is less about the headline term “security” and more about clarity before the search begins. When a hard-to-find IC, connector, module, memory device, relay, switch, MOSFET, diode, or board-level assembly support component is needed quickly, ambiguity can create two risks at once: the wrong part may look acceptable on paper, and the right part may be delayed while teams re-ask basic questions.
PCX can help sourcing teams evaluate options more effectively when the RFQ includes the practical boundaries: acceptable manufacturers, approved alternates, lifecycle status concerns, traceability needs, packaging requirements, test or inspection expectations, and escalation contacts. The PCX Star Quality Control Program is relevant here because speed and savings still have to pass through disciplined review. The sourcing file gives that review a clearer starting point because it records security-relevant acceptance criteria before price, lead time, or alternate availability dominates the conversation.
It also keeps the commercial conversation grounded. A sourcing partner should not promise that a file proves provenance, cybersecurity posture, compliance, or uninterrupted availability. The right posture is more disciplined: use the file to narrow the search, identify evidence gaps earlier, and decide which offers deserve deeper quality or engineering review.
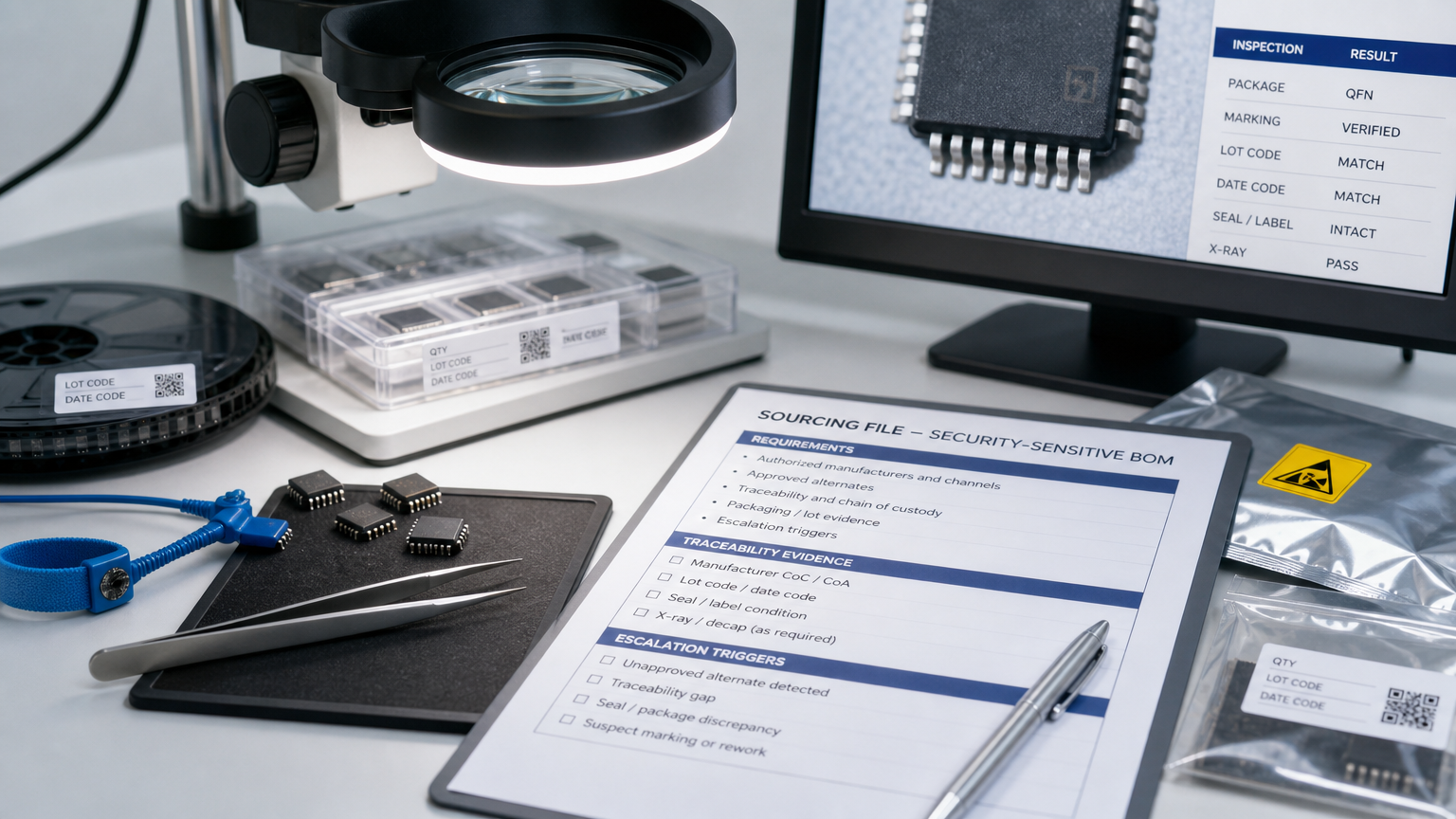
What belongs in a security-sensitive sourcing file
A useful file can be short. It should be specific enough that a buyer can send it with an RFQ and a quality reviewer can understand the boundaries without reconstructing the design history.
- Approved manufacturer part numbers, alternates, package options, temperature grades, and revision constraints.
- Application context: where the part sits in the product and whether failure, substitution, or uncertain provenance creates elevated risk.
- Lifecycle status notes: active, NRND, EOL, last-time-buy history, redesign timing, and known cross-reference limits.
- Traceability expectations: manufacturer labels, lot/date-code information, packaging photos, certificates, chain-of-custody needs, and receiving inspection requirements.
- Quality and handling requirements: ESD packaging, moisture sensitivity, storage limits, functional test expectations, and any destructive-test thresholds.
- Escalation rules: when procurement can proceed, when engineering must approve, and when quality must reject or hold a lot for further review.
NIST’s cybersecurity supply chain risk management materials are useful background because they frame risk across the product and service supply-chain lifecycle, including acquisition and maintenance. NIST also lists risks such as counterfeits, unauthorized production, tampering, theft, malicious hardware or software, and poor manufacturing or development practices. For component buyers, the safe takeaway is not that every sourcing event carries the same risk. It is that acquisition is part of the risk lifecycle, so procurement evidence deserves structure.
The file should also separate must-have requirements from preferences. If a connector color, passive tolerance, or date code range is only preferred, say so. If an IC revision, memory grade, or FPGA package is mandatory, say that clearly. Precision makes it easier to search broadly without weakening the product’s acceptance criteria.
Where buyers should be careful
The sourcing file is a control aid, not a guarantee. Buyers should be careful not to treat a familiar manufacturer name, a clean-looking label, or a fast available offer as proof that the lot is appropriate for a sensitive build. They should also avoid treating any single document as enough when the risk profile calls for layered verification.
For security-sensitive BOM lines, the review should ask a few practical questions. Is the offered part in the approved manufacturer list? Does the package, grade, and revision match the approved drawing or AVL? Are alternates documented, or would accepting one require an ECO? Does the supplier provide enough traceability and packaging evidence for the receiving process? Is the date code acceptable for the application and storage history? Would a shortage-driven spot buy change the inspection level?
This is also where PCX certification and quality context can help buyers think about the evidence they want attached to a shipment. Certifications and documented quality processes matter because they make expectations visible; they should still be matched to the specific product, customer requirement, and component risk.
Turning the security file into an RFQ
An RFQ for a sensitive BOM line should include more than the part number and target quantity. It should include the approved alternates, required condition, unacceptable substitutions, requested documentation, date-code guidance, urgency, and the name of the person who can approve exceptions. If the need involves obsolete or long-lead integrated circuits, FPGAs, microcontrollers, memory, connectors, passive components, or discrete semiconductors, note whether a redesign path exists or whether the current build must stay exact.
That information lets a sourcing partner screen options before the buyer spends time on offers that cannot pass review. It also helps PCX identify when a request belongs in a normal availability search, a lifecycle review, a hard-to-find sourcing effort, or a quality-sensitive escalation.
When the file is ready, buyers can send the requirement through the PCX parts request form with the evidence and exception rules attached. The goal is not to make urgent sourcing feel risk-free. The goal is to make the tradeoffs visible early enough that speed, cost, documentation, and quality can be considered together.

